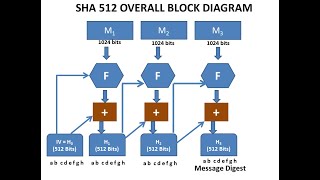
SHA-512 ALGORITHM || SECURE HASH ALGORITHM || CRYPTOGRAPHIC HASH FUNCTIONS || NETWORK SECURITY
Вставка
- Опубліковано 8 жов 2024
- Secure hash algorithm(SHA)-512 implementation with block diagram, round function and generation of words from the text etc.It is a cryptographic hash algorithm and it is authentication algorithm.








Crystal clear explanation, no doubts Thank you sir!
cls room lo ardam kanidi meeru easy ga cheparu sir
very nice lectures clear and easily understandable thank you sir!
Sir,I have subscribed.keep doing.explain everything in detail. I like your explanation
Thank You very much sir
Thank you sir ❤
thank you
Thank you soo much sir You Helped me a lot
Sir very good explanation
sir please do videos on network programming
👍
Sir me tarwate averayna super at explain
Best Lecture
thank you sir .. your explanation is good, please improve the audio quality
Tq for ur suggestion
❤️❤️❤️
Thank u very much sir