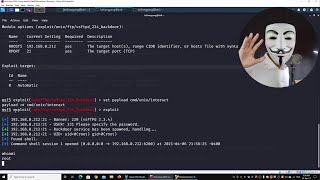
Metasploit For Beginners - How To Scan And Pwn A Computer | Learn From A Pro Hacker
Вставка
- Опубліковано 5 лют 2025
- // Membership //
Want to learn all about cyber-security and become an ethical hacker? Join this channel now to gain access into exclusive ethical hacking videos by clicking this link: / @loiliangyang
// Courses //
Full Ethical Hacking Course: www.udemy.com/...
Full Web Ethical Hacking Course: www.udemy.com/...
Full Mobile Hacking Course: www.udemy.com/...
// Books //
Kali Linux Hacking: amzn.to/3IUXaJv
Linux Basics for Hackers: amzn.to/3EzRPV6
The Ultimate Kali Linux Book: amzn.to/3m7cutD
// Social Links //
Website: www.loiliangya...
Facebook: / loiliangyang
Instagram: / loiliangyang
LinkedIn: / loiliangyang
// Disclaimer //
Hacking without permission is illegal. This channel is strictly educational for learning about cyber-security in the areas of ethical hacking and penetration testing so that we can protect ourselves against the real hackers.