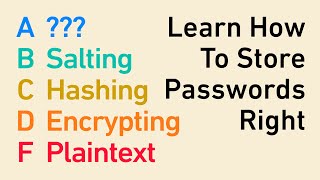
Hashing passwords with Python and Bcrypt
Вставка
- Опубліковано 20 лип 2024
- Enjoying this type of content? Head over to my website at pythonise.com for full length text based tutorials, courses and guides.
Want to help me make even better content? You can by supporting me on Patreon! / juliannash








Thanks, I use these sort of things all the time in my python homework to surprise my teacher and I think this is awesome.
I've just come across this video and found it very clear and useful. Now subscribed and looking forward to learning more about Python. Thanks Julian!
Awesome! Welcome on board!
Great tutorial! Thank you. Also just subscribed and hopefully you gonna make more tutorials.
Thank you very much for this video, I have been struggling for 2 hours now, I wish I had watched this video earlier!
Thank you very much for this. But how would you hide the password in the source code of your web-page? Would it be enough to create a dummy page with the password and to import the hashed password in the main code of the application?
Awesome tutorial!
Thanks, was facing that problem discussed in video at 5:30. It was really helpful.
with like a Tkinter Entry its
input = Entry1.get()
cryp = bytes(input, encoding="utf-8")
result = bcrypt.hashpw(cryp, bcrypt.gensalt())
print(result)
THANK YOU VERY MUCH! Helped a lot ! Thanks again !! :)
great content bro keep it up, ill be subscribing
Fantastic explanation thanks a lot!
Cheers dude!
I get error "invalid salt" in checkpw. I m writing a code for password authentication using socket programming in python.
Damn bro you explained this so well I'm gonna hash everything now
is there any way you could drop a tutorial similar to this that would include peppering
Great video
i must crypt some fields in db with python can i use the method who yyou show in this video ?
thanks for the tutorial...
You're welcome! Glad you enjoyed it
Thanks a thousand!!!!!!!!!
How we can hash the user input password???
I get what this python tutorial and the lines of this script, thanks. But I am confused how this can be implemented in a production environment. Let's say I have an API key. I will use this to obtain a hashed API key and save it somewhere. In run time, do I ask user to enter the original string of the API key, and then I will hash this user-input API key, and then compare the newly hashed API key vs. the stored hashed API key? If so, how can I be sure when I use `bcrypt.hashpw()` on the newly entered API key, the resulting hashed string will be the same as the stored one? Can/should I save the `hashed = bcrypt.hashpw(password, bcrypt.gensalt())` inside the project directory, so when I hash the new API key, it should result the same hashed string?
If I have access to the hash file, why don't I just replace it with Hashes that I know??? Then access the system with my own set of passwords populating it...
What app where you typing on before python ???
How would i pass in a user input as the password? I keep getting the "TypeError: can only concatenate str (not "bytes") to str" error. Would it have to be something like
username = input("username: ")
Or would something need to go before it?
import bcrypt
password = input("password: ")
hashed = bcrypt.hashpw(password.encode('utf-8'), bcrypt.gensalt())
print(hashed)
Can anybody tell me, what do you save on the database?, the varible "hashed" that he creates on the video?
Yes
How decode this hash password ??
hey how to do that if password was taken from input ??
password = input().encode("utf-8")
if hashing is irreversible how checkpw checks if our password matches hash? don't get it
The password typed in by the user is hashed, this is compared to the stored hash.
@@NotKewl but it is hashed with random salt, so how later can be it compared?
i dont get it as well, randomly spotted your comment while was watching yt and looking for an answer
It won’t work unless the salt is the same, otherwise you just end up with a completely different hash each time that can’t be compared. Usually the salt would be generated once and stored as an environment variable on the server.
@@djadamkent but it actually works
where did Julian go?
I do not like the idea of having to grab the password from the database in order to run a check
Hey i have a question
Shame that you stopped uploading tbh😢
Got some new videos coming next week!
Salting ensures that no 2 same passwords are the same hash.